Code-JSON
Screen Watermark Solution Enterprise
Multi-Platform Screen DLP, Anti-Screenshot & Forensic WatermarkingxSecuritas Screen Watermark Enterprise is an advanced screen security and anti-screenshot solution that embeds visible and invisible watermarks, blocks screen-capture tools, supports VDI and RemoteApp environments, and integrates with Microsoft Sensitivity Labels and Active Directory. It helps organizations prevent screen-based data leakage across Windows, macOS, Linux, and hybrid work environments.
Trusted by more than 350,000 users worldwide for over five years, xSecuritas Screen Watermark is used by banks, government agencies, defense organizations, telecom providers, and global enterprises that require strong data-protection and compliance-ready security.
xSecuritas is certified with ISO 27001:2022 and SOC2 Type II, confirming that our security controls, development processes, and operational practices meet internationally recognized standards. These certifications provide additional assurance for enterprises that require strict compliance and secure handling of sensitive information.


About xSecuritas Screen Watermark
Adaptive Watermarking to Prevent Screen-Based Data Leakage
xSecuritas Screen Watermark helps organizations prevent screen-based data leakage by blocking screenshots, embedding visible and invisible watermarks, and displaying dynamic user-specific metadata. Administrators can choose when watermarks appear—always, only in certain environments, or only when sensitive data is accessed.
Customizable Metadata Watermarking with Extensive Attribute Support
The system supports more than 30 metadata types including user ID, IP address, MAC address, date/time, Active Directory attributes, and Microsoft Sensitivity Labels (Data Classification). These can be shown as text, images, or QR codes with customizable size, opacity, color, repetition, and angle.
Web-Based Policy Management with AD Integration and Flexible Deployment
Policies are created and managed through an intuitive web-based policy server and can be linked to Active Directory for automated assignment to users, groups, or organizational units. xSecuritas products are trusted by over 350,000 users worldwide and are available in both cloud and fully on-premise configurations (no Internet required).
Key features of the agent program
Dynamic On-Screen Watermarking
- Show or hide watermarks based on environment, network type, location, ICMP accessibility, remote/local session, or corporate policies.
- Watermarks can be applied always, selectively, or only when sensitive data is accessed.
Advanced Metadata Watermarks
- Supports over 30 types of metadata for dynamic watermarking
- User ID, computer name, Local & remote IP address, MAC address, Date & time
- Active Directory attributes, Microsoft Sensitivity Labels (MIP Data Classification)
- Text, image, and QR-code watermarks
Multiple Watermark Display Modes
- Display on all monitors or only selected monitors
- Desktop-level (global) watermark
- Window-level (per-application) watermark
- Application & website allowlist/denylist (blacklist/whitelist)
- “Show only on specified apps/sites” or “Hide only on specified apps/sites”
Support for VDI / RemoteApp / Virtual Environments
- Watermarks work even without installing an agent on the client PC
- Support Microsoft Remote Desktop / RemoteApp, Citrix XenDesktop / XenApp, VMware Horizon VDI & Apps, Dizzion Frame, Other VDI-based environments
Invisible (Hidden) Watermark
- Invisible watermark is embedded into captured images automatically
- Not visible to users
- Administrators can extract it using a dedicated tool
Microsoft Sensitivity Label (MIP) Integration
- Display or hide watermarks based on MIP labels
- Apply policy only to specific sensitivity levels
- Supports Office 365, SharePoint Online, and OneDrive
- Real-time label detection on Word/Excel/PowerPoint and browser-based apps
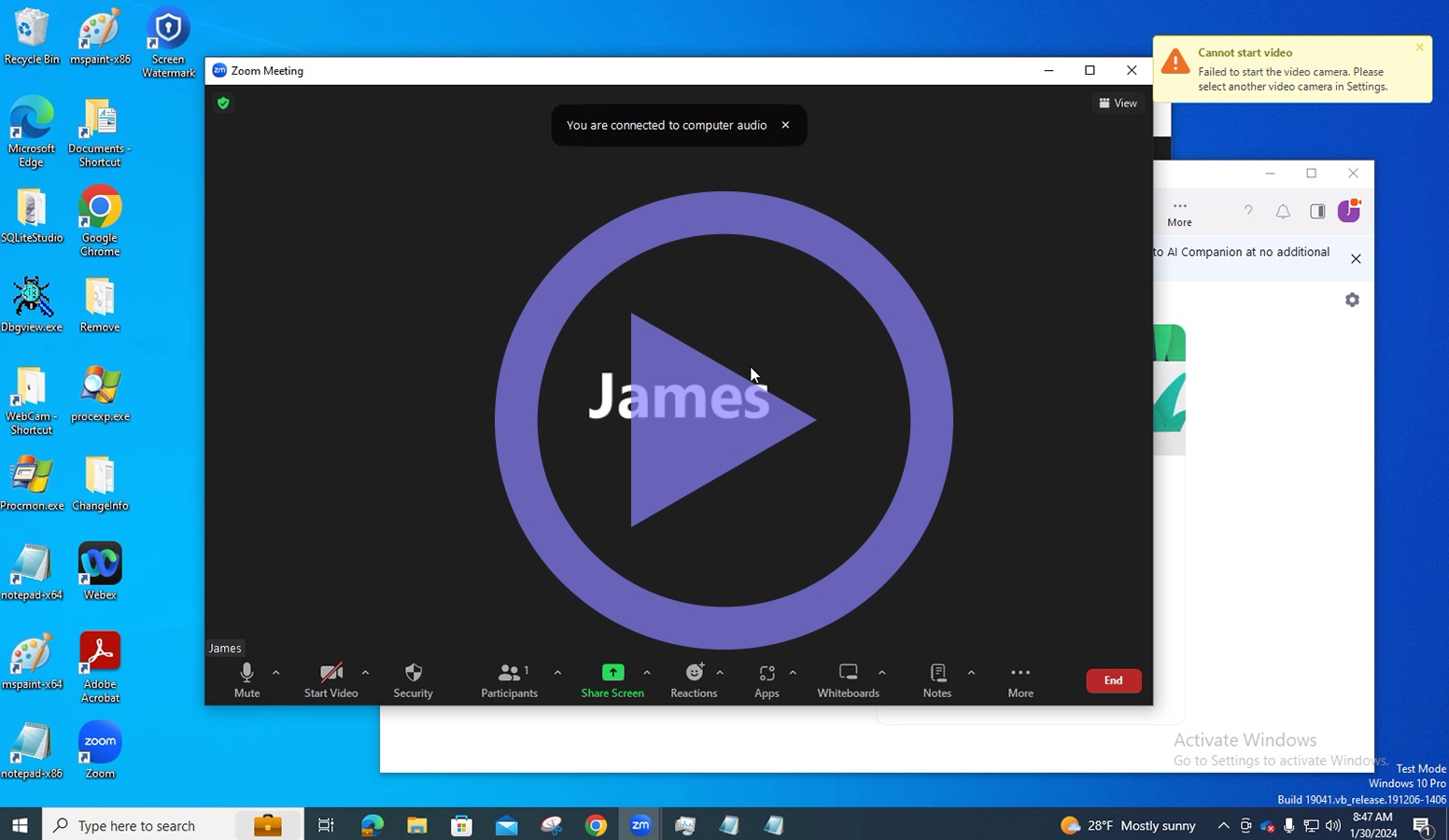
Video Conferencing Watermark
- Applies watermarks during screen/contents sharing
- Supported platforms: Zoom, Microsoft Teams, Cisco WebEx
- Works on full screen sharing, window sharing, and content sharing
- Prevents screen leakage during virtual meetings
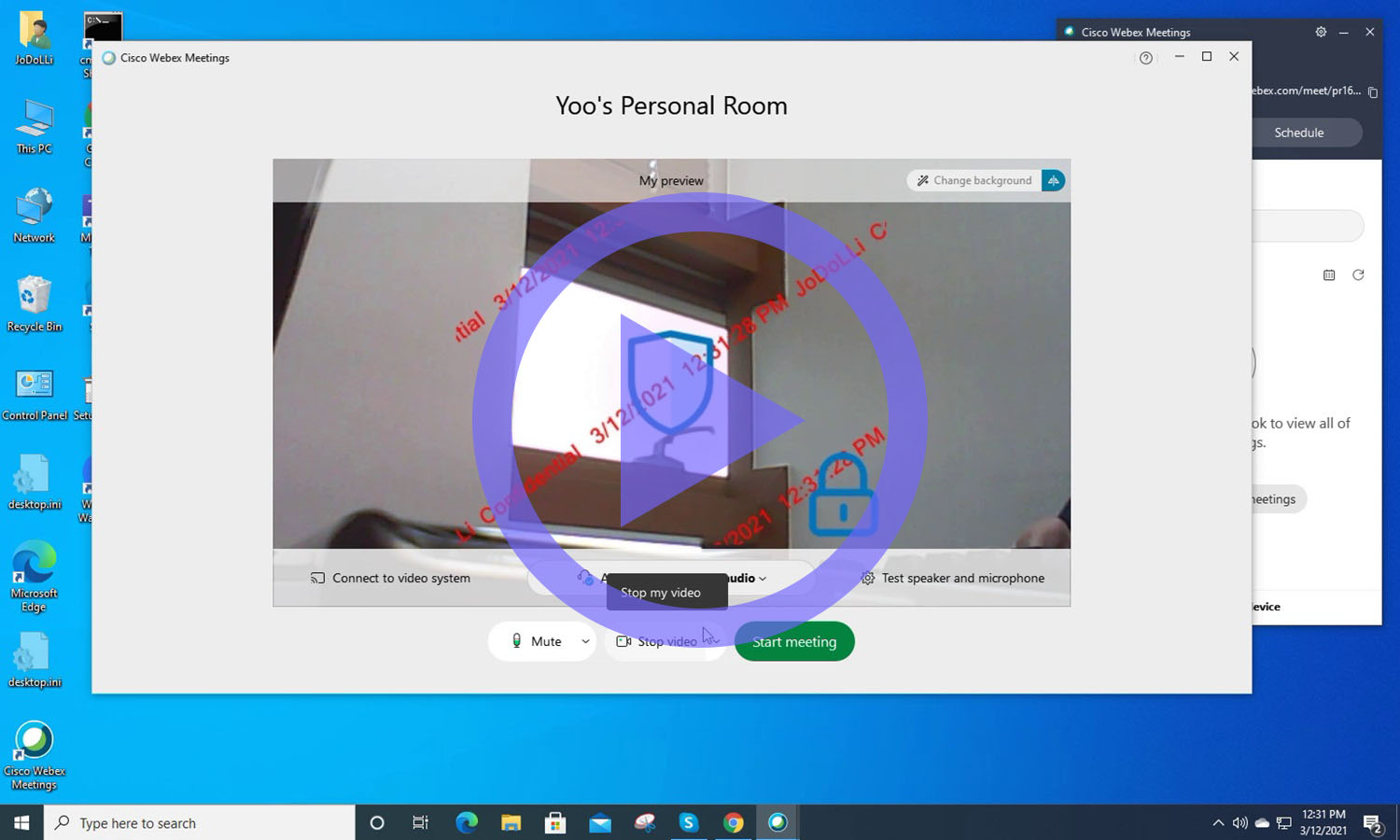
Webcam Watermark (Add-On)
- Applies watermark to live webcam video streams
- Display desired text/image watermark directly on the webcam feed
- Watermark appears on both host and participant video screens
- Supported providers: Zoom, Microsoft Teams, Cisco WebEx
- Same styling & metadata rules as screen watermark
- Works during video conferencing
Screen Capture Blocking
- Blocks OS screenshot tools (Snipping Tool, PrintScreen, etc.)
- Blocks 3rd-party capture apps
- Prevents window-specific capture
- If capture occurs, the image can be saved to a server or emailed to admin
Environment-Based Policy Control
- Flexible watermark behavior based on:
- Office vs home network, IP allowlist/denylist, ICMP reachability
Print Watermark Function (Add-On)
- Adds visible watermarks to printed documents
- Print Logs user, document name, page count, printer etc
- Disable/allow printing based on printer, process, document type
- Optional print blocking or forced watermark
Self-Protection / Tamper Protection
- Agent cannot be killed via Task Manager or 3rd party tools
- Files cannot be deleted via Explorer or 3rd party tools
- Prevents unauthorized uninstallation (requires admin password)
- Auto-start with OS and cannot be disabled by users
- Optional hidden mode (tray icon hidden)
Key features of the policy server
Enterprise Watermark Policy Management with Flexible Deployment and Advanced Access Contro
- Cloud or on-premise (no Internet required for on-prem)
- Create, deploy, and manage watermark policies
- Control remote agents (quit, uninstall)
- Assign policies by department (AD-OU), user, IP address, AD group, or domain
- Reservation/scheduled policies supported
- Preview watermarks before deployment
- Centralized logging and reporting
- Supports Microsoft Active Directory login
- Supports SAML-based Single Sign-On (SSO) for enterprise identity providers
- Supports Two-Factor Authentication (2FA) to strengthen admin-level security
How xSecuritas Screen Watermark Enterprise Works
Architecture Overview (Agent ↔ Policy Server)
- Agent (Windows / macOS / Linux / VDI Host)
- Identifies device/user attributes (User ID, Hostname, AD attributes, IP/Subnet, Microsoft Sensitivity Label, etc.)
- Generates the watermark overlay using GPU or OS-level rendering layers
- Retrieves the latest policy from the Policy Server using a secure pull model
- Detects screenshot, print, and webcam access events
- Encrypts and uploads security events and forensic logs to the Policy Server
- Policy Server (Cloud or On-Premise)
- Maps policies by AD OU, user, group, domain, or IP address
- Manages watermark templates, metadata rules, and environment logic
- Tracks Agent status and supports remote quit/uninstall
- Stores logs, forensic data, and audit records in centralized storage
Workflow for RemoteApp / XenApp / Horizon / Frame
- The Agent is installed only on the RemoteApp/XenApp server, not on the user’s PC.
- When a user opens Word/Excel/Browser inside the RemoteApp session, the watermark overlay is rendered inside the virtual window.
- Watermarks appear consistently even if the user’s endpoint does not have the Agent installed.
- Policy Server automatically assigns watermark policies based on domain, IP, OU, or user identity.
- Screenshot permissions are evaluated based on server-side rules and client communication.
- Invisible Watermark is automatically embedded in captured images even in RemoteApp sessions.
Policy Server Controls
- When an admin saves a policy, all Agents update automatically based on their polling interval
- Multiple policies can be created for departments, groups, users, or IP ranges
- Administrators can remotely terminate or uninstall Agents
- Real-time monitoring shows Agent connection status, active policies, and version info
- Event logs (screenshot, print, webcam) are centralized and searchable in the Policy Server
Agent Installation, Auto-Update & Remote Removal
- Automated Agent Updates (Windows / macOS / Linux)
- Enterprise Deployment via SCCM / MDM
- Remote Removal & Bulk Uninstallation
Environment-Aware Policy Logic
- Corporate network vs external network → watermark mode switches automatically
- ICMP/Ping availability is used to detect office vs remote conditions
- IP/Subnet changes trigger policy reassignment or text/metadata adjustments
- AD security group changes dynamically update corresponding watermark policies
- System differentiates between Remote Desktop vs Local Desktop automatically
Workflow on Local PC or VDI Host
- The user installs the Agent (or it is auto-launched on a VDI host).
- The Agent registers with the Policy Server and downloads the assigned policy.
- Each policy contains display text, transparency, repetition pattern, QR/image options, colors, position mapping, and Sensitivity Label rules.
- The Agent analyzes OS resolution, multi-monitor layout, and DPI scaling to render the watermark at optimal coordinates.
- If the network is interrupted, the Agent continues operating using the last cached policy (offline fail-safe mode).
- Screenshot actions (Win+Shift+S, PrtScn, Snipping Tool), print jobs, or webcam usage events are detected and logged.
- Logs are sent to the server immediately or in scheduled batches based on configuration.
- Administrators can view watermark status, device connections, and security events per user or machine.
Security, Logging & Compliance Engine
- Screenshot, print, and webcam events are locally encrypted before transmission
- The server correlates events with AD identity, session ID, and assigned policies
- Administrators filter logs by time, device, application, process, and policy
- Invisible forensic watermark embeds a unique correlation code inside captured images
- Even if a screenshot leaks externally, the server can trace the exact user and device
High-Availability & Fail-Safe Mode
- If Agent loses connection to the server, cached policies remain active
- Watermarks continue to display without interruption
- Once the server becomes available, the Agent automatically resynchronizes
- Remote uninstall/quit commands are queued and executed after reconnection
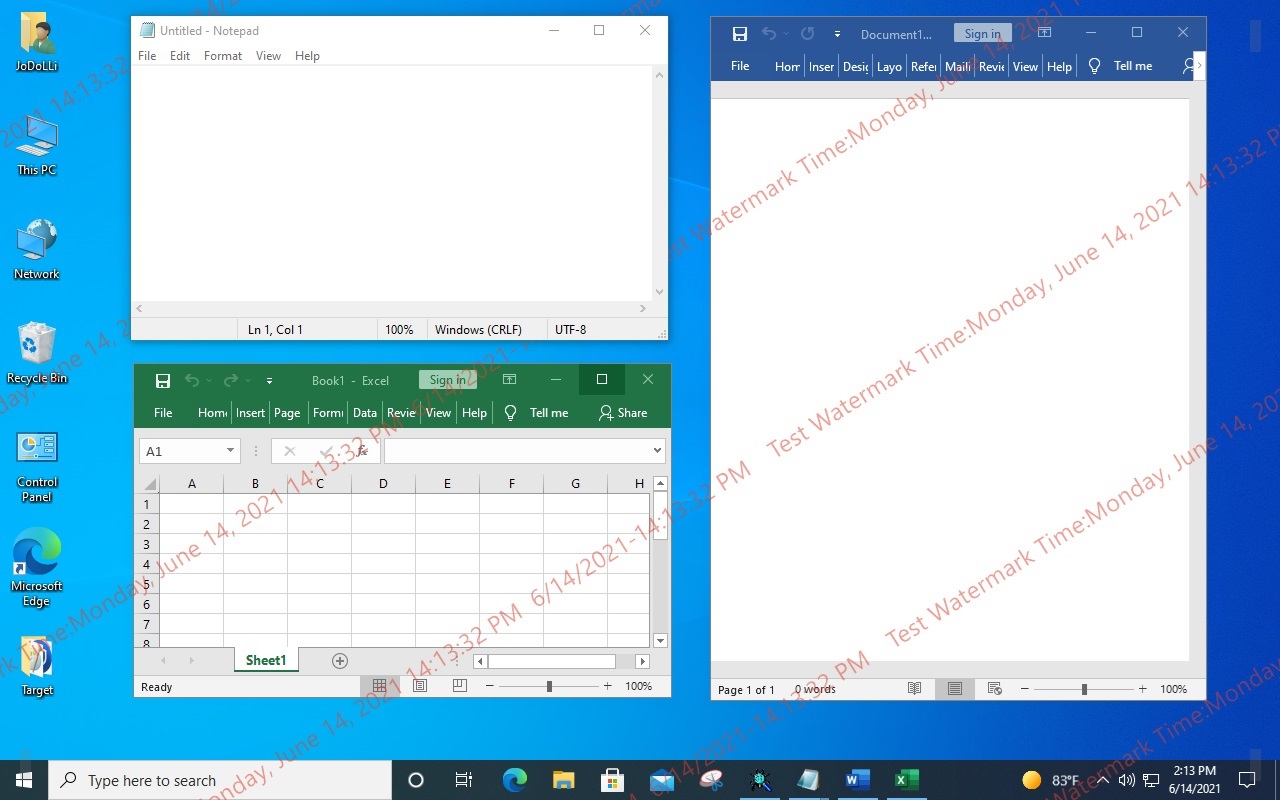
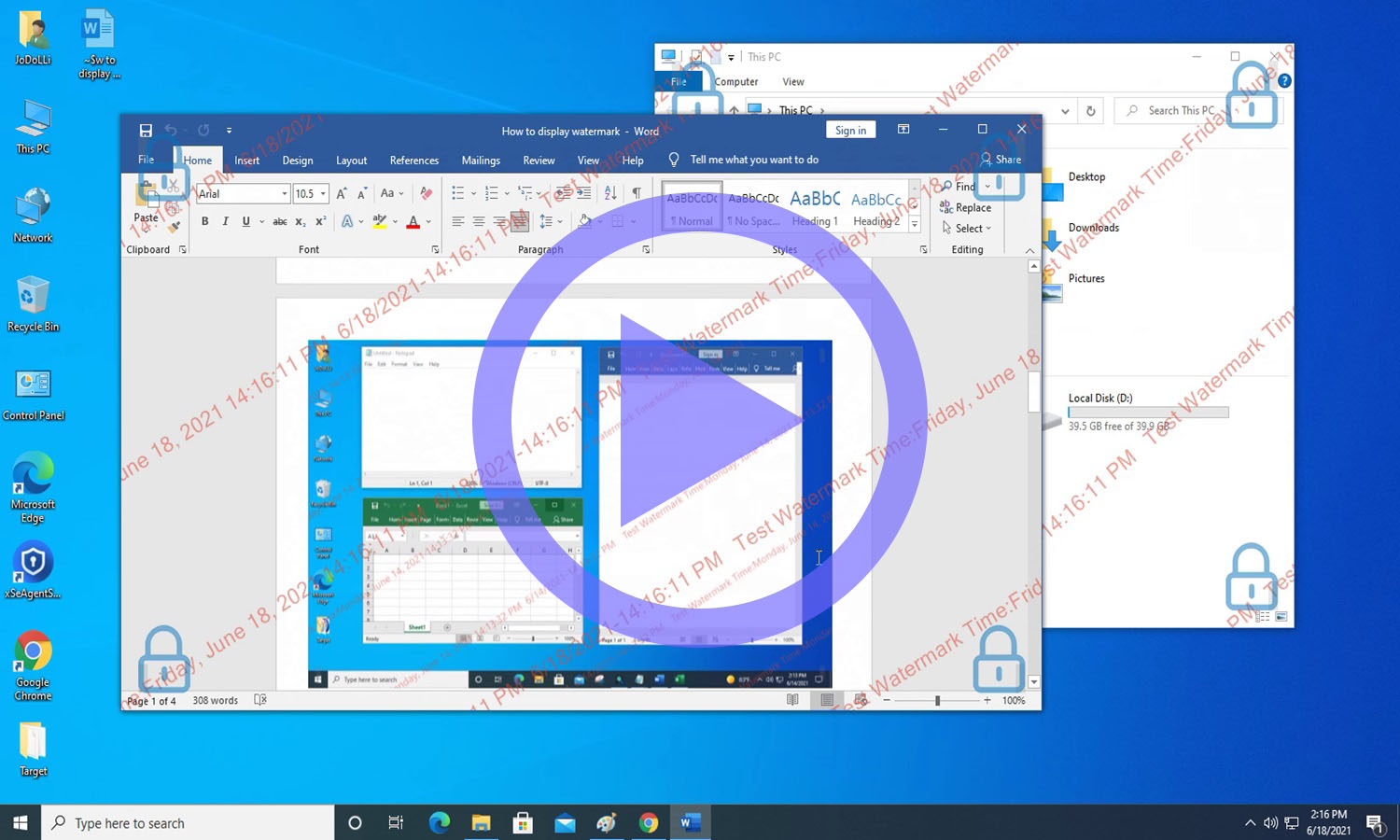
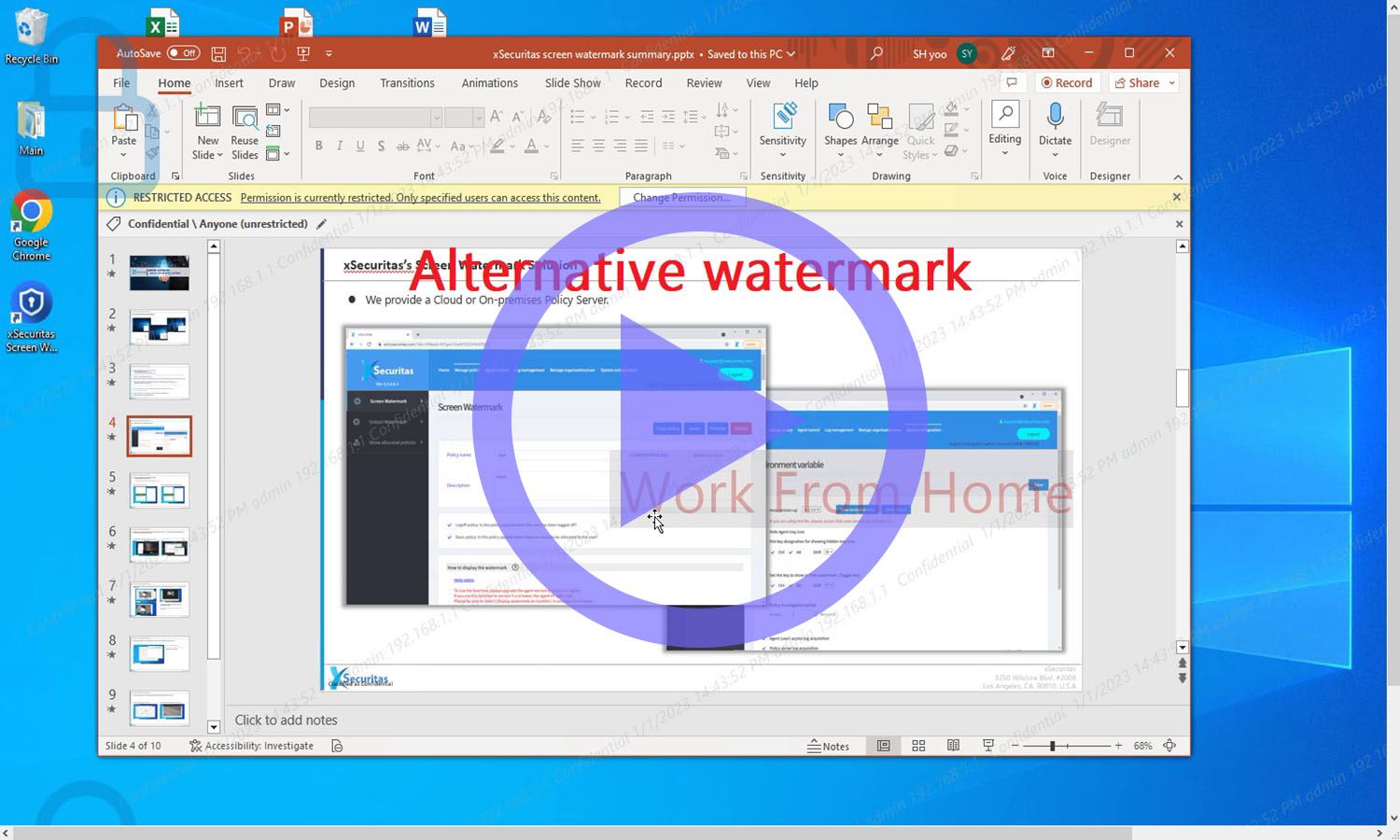
Screen Watermark Video Demonstrations
xSecuritas Screen Watermark supports four flexible ways to display watermarks:
- Watermarks can appear on all monitors or only selected monitors
- Display watermarks on the desktop and within individual application windows
- Show watermarks only on specific applications or websites
- Hide watermarks only for designated applications or websites
- These options allow organizations to apply precise, environment-based watermarking.
Webcam Watermarking for Secure Video Conferencing
- Webcam Watermark for Video Conferencing
- Adds a webcam watermark to both the host and participant video streams
- The webcam watermark uses the same metadata and styling rules as the screen watermark
- Fully supports Zoom, Microsoft Teams, and Cisco WebEx
- Ideal for preventing data leakage during virtual meetings.
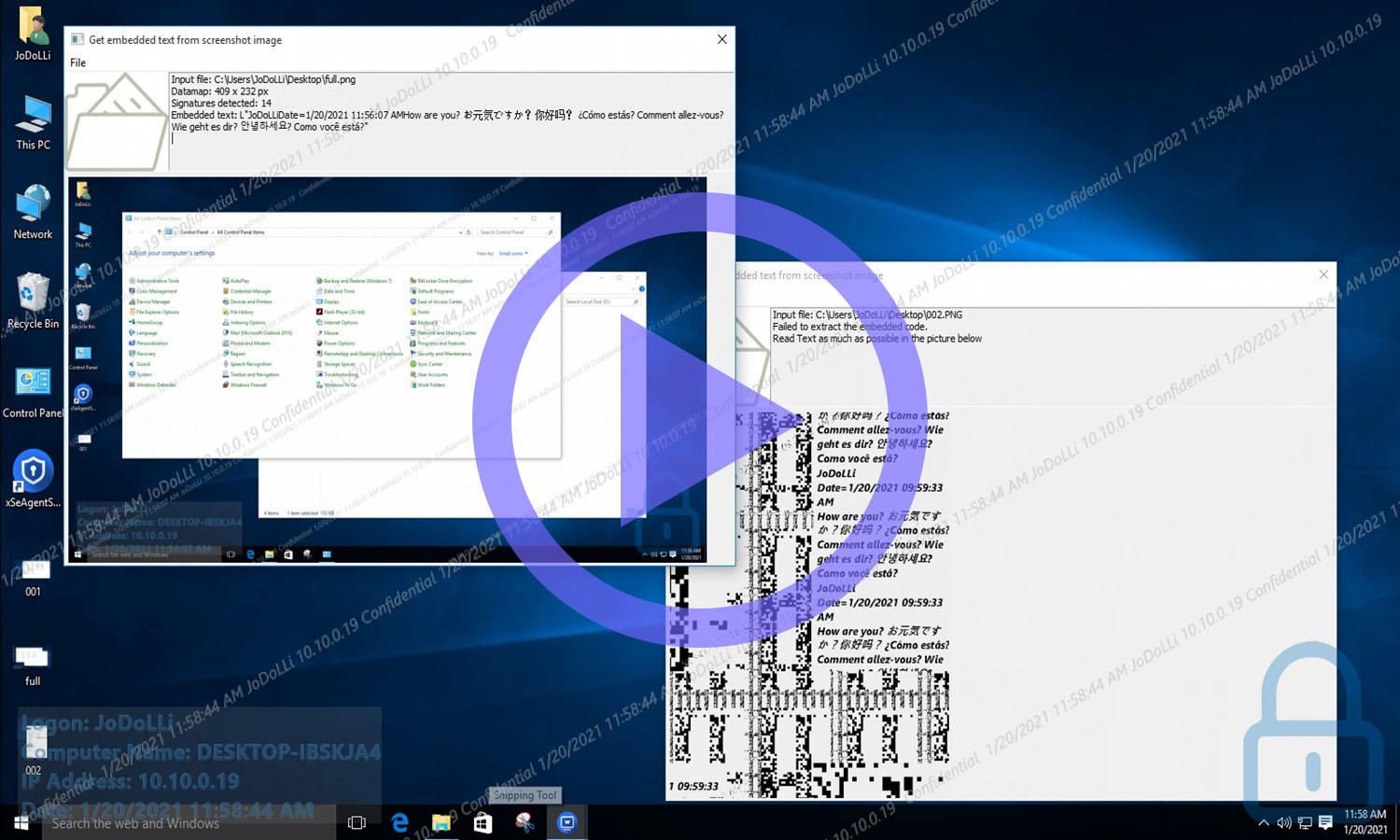
Invisible Encrypted Watermarks for Forensic Screenshot Tracking
- Invisible (Hidden) Watermark in Captured Screenshots
- When the screen is captured, an invisible encrypted watermark is automatically embedded
- The watermark is not visible to users, but admins can extract it using a dedicated tool
- Encryption keys vary per customer for enhanced security
- This provides strong forensic tracking for compliance
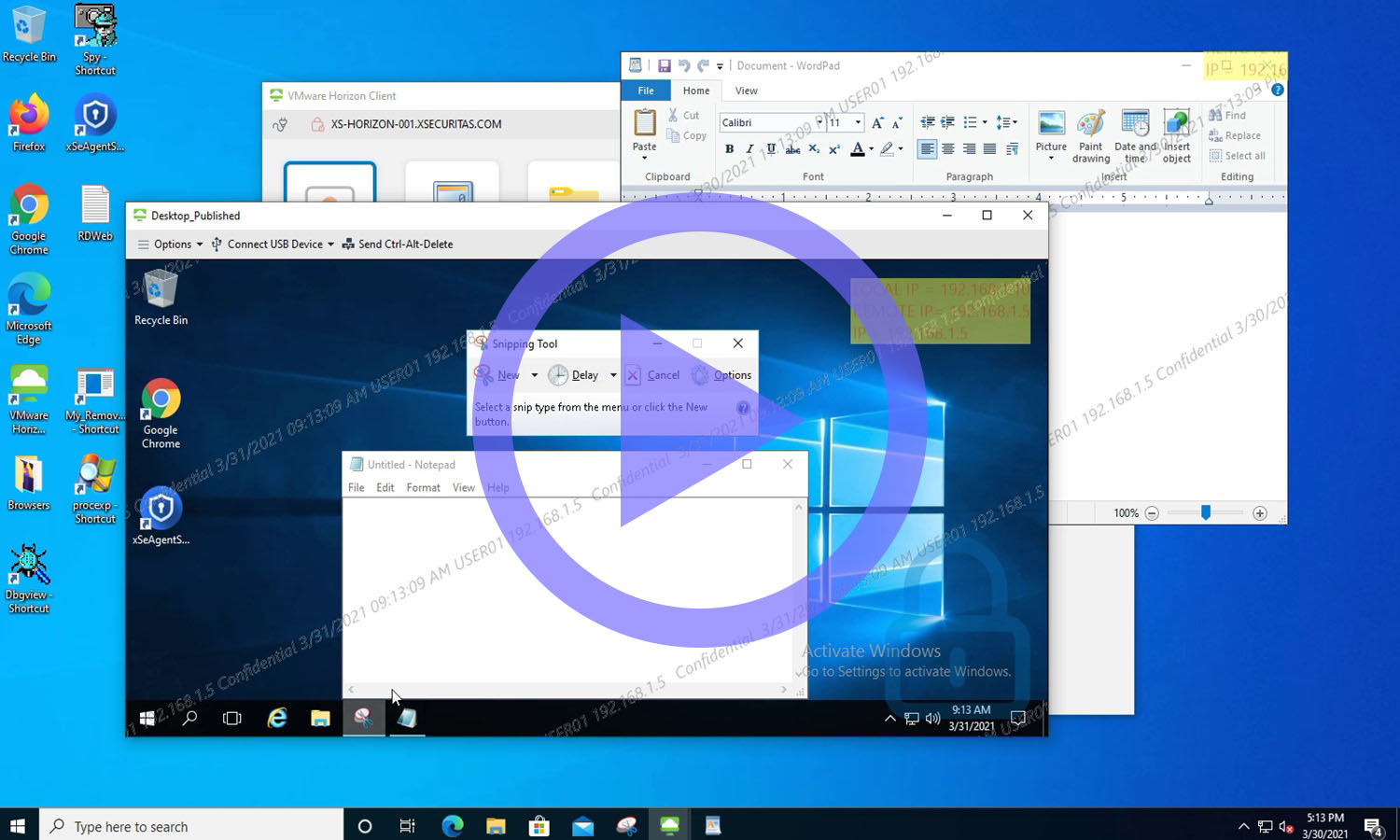
Environment-Aware Watermarking with Agentless VDI Support
- Environment-Based Watermark Behavior & VDI Support
- Watermarks can appear only in specific environments (e.g., visible at home, hidden at office)
- Supports RemoteApp, XenApp, and Remote Desktop without installing an agent on the client PC
- Perfect for hybrid work environments.
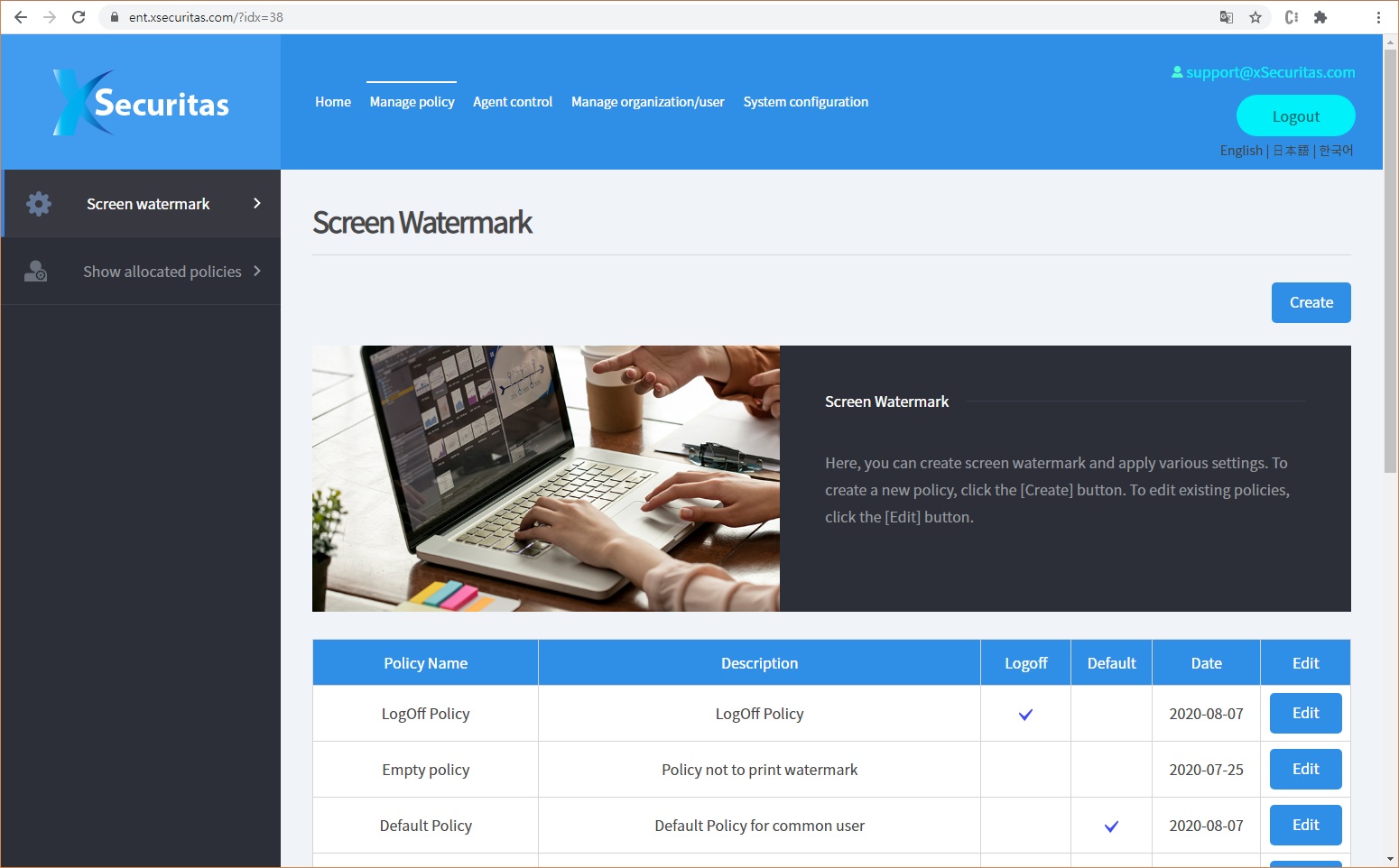
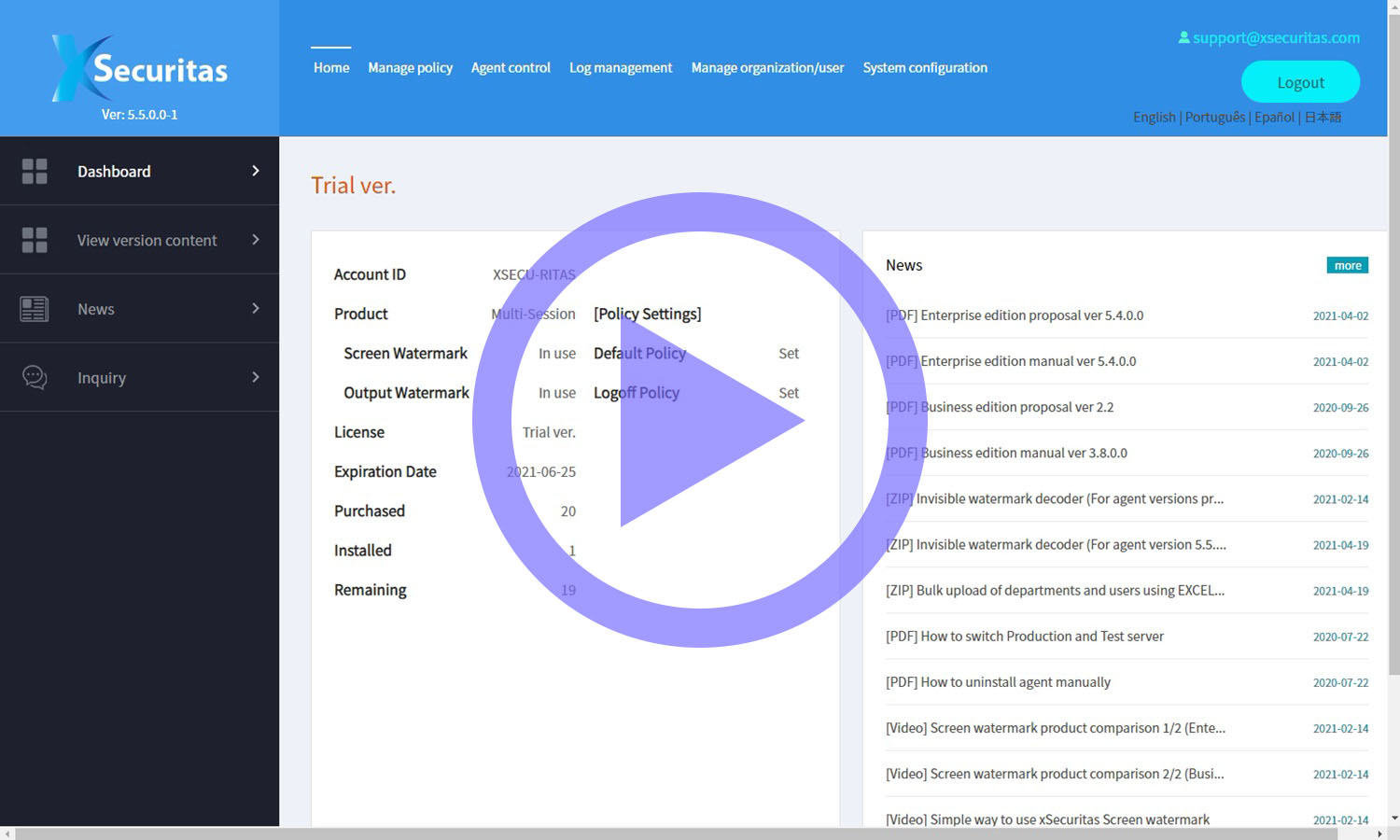
Screen Watermark Quick Start for Administrators
- Quick Start Guide for Screen Watermark
- A simple guide showing how to install the xSecuritas Screen Watermark Agent
- Demonstrates how to configure and manage policies using the Web Policy Server
- Useful for first-time administrators
Comprehensive Screen Capture Prevention and Monitoring
- Screen Capture Protection
- Prevents users from capturing the entire screen
- Blocks capturing of specific application windows
- If a capture is attempted, the image can be stored on a server or emailed to an administrator
- Helps organizations prevent unauthorized screenshots
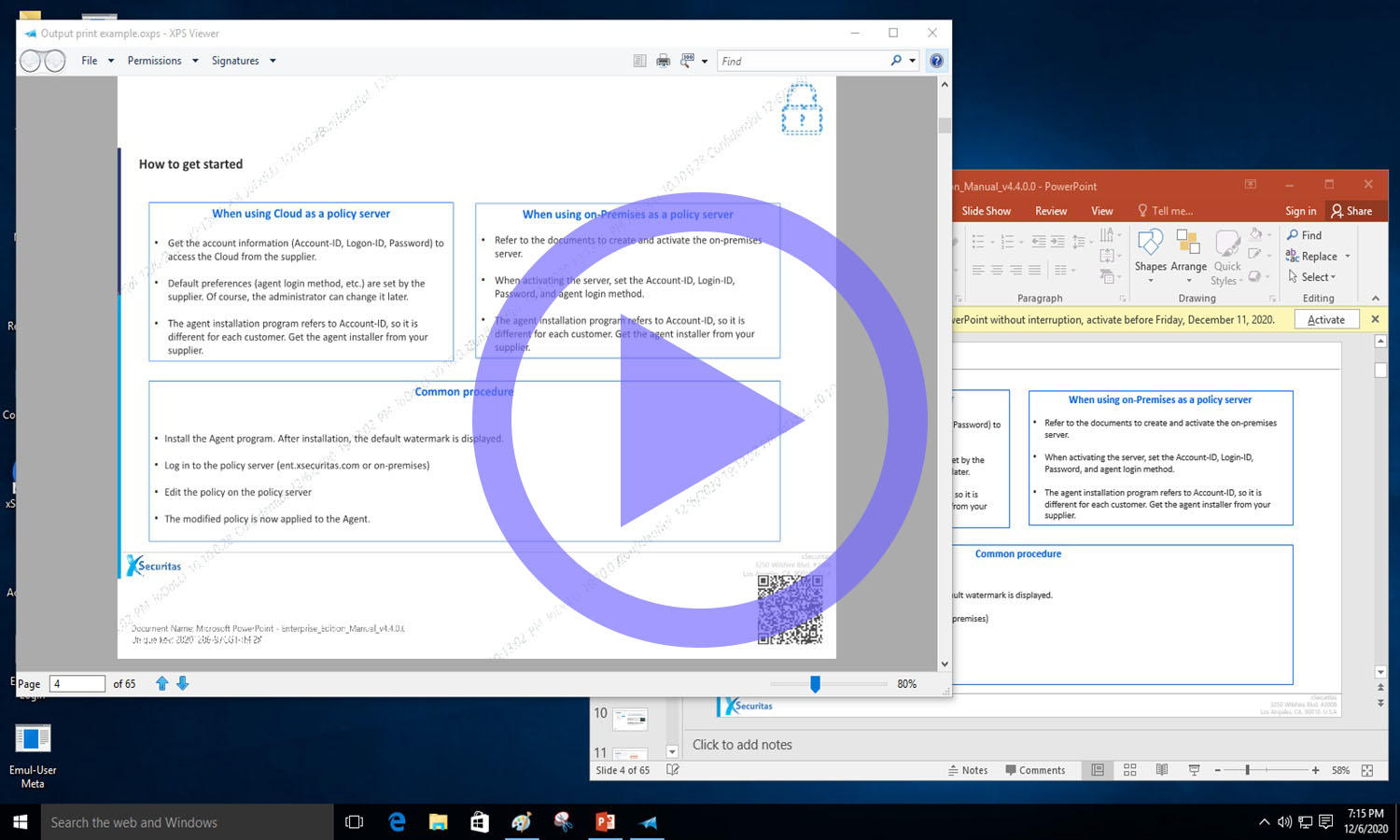
Print Watermarking and Activity Logging for Enhanced Document Security
- Print Watermarking & Print Logging
- Automatically adds a visible watermark to printed documents
- Logs print activity: user name, document name, printer, pages, timestamp
- Admins can allow or block printing based on printer, process, or document type
- Strengthens print security in sensitive environments
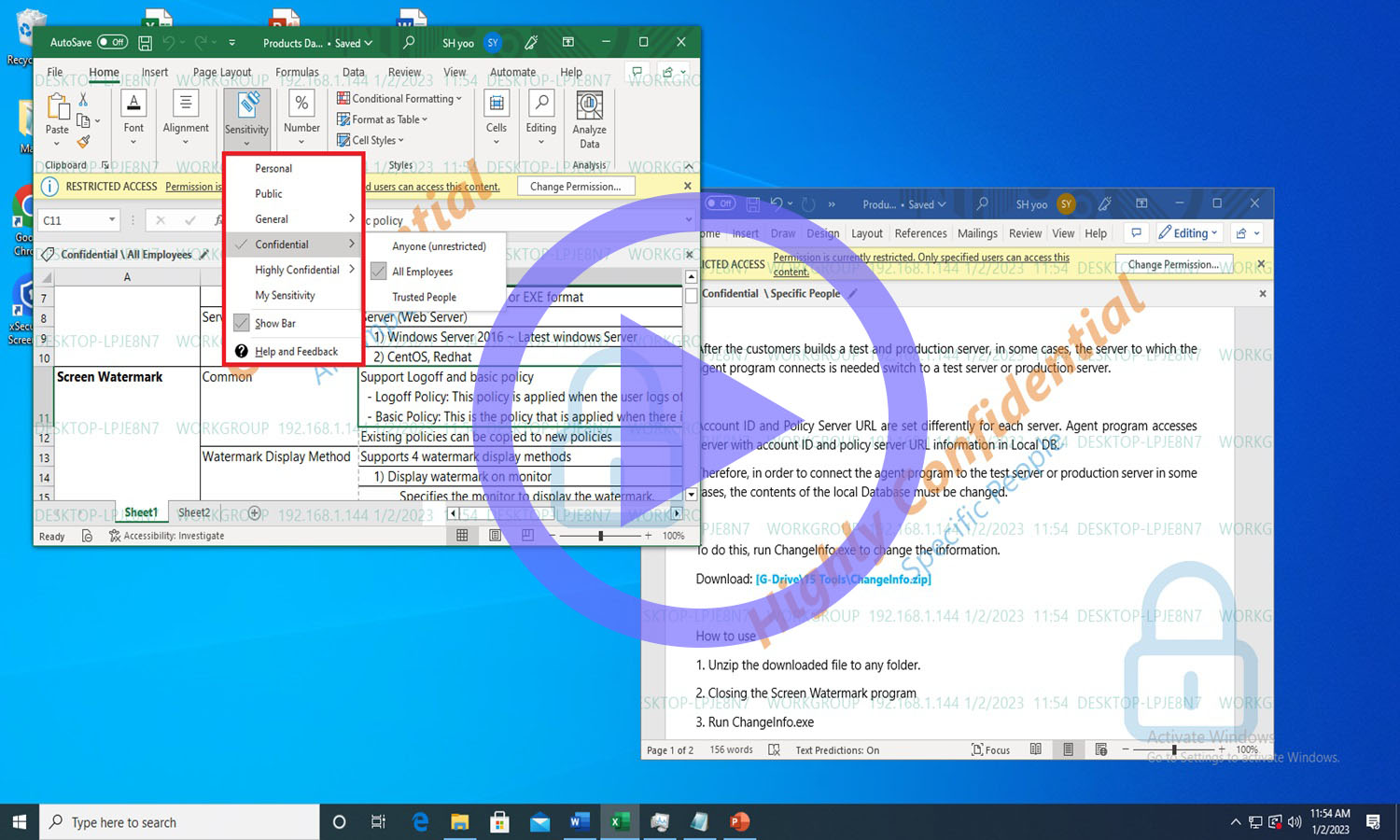
Watermark Controls Integrated with Microsoft Sensitivity Labels
- Microsoft Sensitivity Label Integration
- Display or hide watermarks based on Microsoft Sensitivity Labels (MIP / Data Classification)
- Apply watermarks only to documents with specific labels
- Supports SharePoint, OneDrive, Office 365 browser apps
- Ideal for organizations with data-classification policies
Dynamic Environment-Aware Watermarking for Hybrid Work Security
- Environment-Aware Watermarking (Office vs Home)
- Watermarks can change dynamically based on: ICMP network accessibility, IP address / subnet, Local vs remote connection
- Helps differentiate corporate vs external device usage
- Useful for hybrid workplace security
Adaptive Screen Watermarking for macOS Environments
- Screen Watermark for macOS
- Supports macOS 10.14 or later
- Show or hide watermarks depending on whether specific apps are running
- Designed to match macOS performance and user experience
- Provides consistent watermarking across multi-OS environments.
Screen Watermark Video Demonstrations
Frequently Asked Questions about xSecuritas Screen Watermark Enterprise Version
What is xSecuritas Enterprise Screen Watermark and how does it prevent screen-based data leakage?
xSecuritas Screen Watermark Enterprise Version overlays visible and invisible metadata watermarks and blocks screenshots or camera capture attempts, preventing unauthorized screen-based data leakage across Windows, macOS, Linux, and VDI environments.
How much CPU does the xSecuritas Screen Watermark Agent use?
Even with complex or high-density watermark configurations, the xSecuritas Agent typically uses 0–2% CPU, ensuring minimal system impact on Windows, macOS, and Linux environments.
Does the solution support invisible (forensic) watermarking?
Yes. xSecuritas embeds an encrypted invisible watermark inside captured images, enabling administrators to trace leaked screenshots back to specific users, devices, and sessions.
Which operating systems are supported by the Agent?
Windows 7/SP1+, Windows Server 2008 R2+, macOS 10.14+, and Linux distributions using glibc 2.17+ (Ubuntu, RedHat, CentOS, Debian, Fedora, OpenSUSE, KDE, etc.).
Does xSecuritas Screen Watermark work in VDI, RemoteApp, XenApp, Horizon, or Frame environments?
Yes. Watermarks render directly inside the remote session even when the user’s local PC does not have an Agent installed.
Does the solution block OS-level screenshot tools (PrintScreen, Snipping Tool, Win+Shift+S, etc.) and third-party screenshot apps?
Yes. The Agent blocks OS screenshot APIs and prevents or logs capture attempts from standard and third-party tools.
Can xSecuritas detect suspicious screen-capture behavior and generate logs?
Yes. All screenshot attempts, blocked captures, and protected content interactions are logged and uploaded to the Policy Server for analysis.
Does xSecuritas integrate with Microsoft Sensitivity Labels (MIP)?
Yes. Watermark visibility and behavior can be dynamically controlled based on Microsoft Information Protection (MIP) labels.
Can I show watermarks only for specific applications or websites?
Yes. You can configure allowlists/denylists so watermarks appear only on selected apps or URLs.
Does the Screen Watermark support multi-monitor and ultra-wide displays?
Yes. The Agent automatically detects monitor configuration, DPI scaling, and layout changes to render watermarks accurately.
What metadata can be displayed in the watermark?
More than 30 types, including user ID, PC name, IP/MAC address, AD attributes, date/time, session ID, QR code, and MIP label.
Does the Agent continue applying policies if the network is disconnected?
Yes. A secure local cache ensures the watermark remains active offline with the most recent policy.
Can the Policy Server assign policies by department, group, user, or IP range?
Yes. You can assign policies by AD OU, AD group, user ID, domain, IP address, or custom mapping rules.
Does xSecuritas support print watermarking and print control?
Yes. Print Watermark inserts visible watermarks based on printer, app, sensitivity label, or user policy.
Does it support webcam watermarking and webcam blocking?
Yes. Webcam watermarks can be applied to live video streams, and webcam access can be restricted by app or website.
Can administrators remotely uninstall or disable Agents?
Yes. With proper permissions, administrators can remotely uninstall, quit, or restart Agents from the Policy Server.
How does the product detect and block unauthorized screen-capture tools?
The Agent intercepts Win32 APIs, DirectX layers, and known tool signatures to block or log unauthorized capture attempts.
Does watermarking work only inside RemoteApp windows without affecting the user’s local desktop?
Yes. Watermarks render specifically within the RemoteApp session window.
Does the solution work without an Internet connection?
Yes. On-premise deployments enable complete offline operation.
Can external contractors or temporary users receive different watermark policies?
Yes. Policies can be dynamically assigned by IP, AD group, domain, device type, or location.
Are screenshot, print, and webcam events stored centrally for auditing?
Yes. All security events are uploaded to the Policy Server and can be searched by user, device, time, or policy.
Does xSecuritas support deep forensic tracking?
Yes. Invisible watermarks + log correlation enable full-screen leakage tracing even for externally leaked images.
Can policies be scheduled or time-based?
Yes. Policies can be configured by time, department, user shifts, or reservation schedules.
Is real-time watermark preview available?
Yes. Administrators can preview watermark appearance directly in the Policy Server.
Does the Agent support automatic updates?
Yes. Windows, macOS, and Linux Agents support secure password-free auto-updates.
Can the Agent be deployed through SCCM, Intune, JAMF, GPO, PDQ, or MDM tools?
Yes. All major enterprise deployment frameworks are supported.
Does the Agent support hidden/stealth mode?
Yes. The tray icon can be hidden, and the Agent can operate in tamper-proof mode.
How does the Policy Server communicate with Agents?
Agents securely pull the latest policies from the server and batch-upload logs using encrypted communication channels.
Does the solution support multi-policy and multi-tenant environments?
Yes. Multiple policies can be created and automatically mapped to organizations, departments, or user groups.
Does the watermark require modifying our applications?
No. Watermark rendering operates independently of application code and requires no modification.
Do the Policy Server and Database Server need to run on the same machine?
They can run on the same server for small or mid-sized deployments.
For environments with over 1,000 users, we recommend separating the Policy Server and Database Server for optimal performance and scalability.
Which database systems are supported by xSecuritas products?
xSecuritas solutions support MariaDB and Microsoft SQL Server (MS-SQL) as the primary databases for the Policy Server and logging system. Both databases are fully compatible with high-availability (HA) deployments and enterprise-scale environments.
Does xSecuritas support High Availability (HA) for enterprise environments?
Yes. Both the Database Server (MariaDB / MS-SQL) and the Web-based Policy Server can be fully configured in High Availability (HA) mode for fault-tolerant, mission-critical environments.
How does xSecuritas handle issues or incidents reported during product operation?
All reported issues are treated with the highest priority. Most problems are analyzed and patched within 1–2 business days. For more complex cases requiring additional time, xSecuritas provides customers with an estimated resolution date and continues to deliver progress updates until the issue is fully resolved.
Is xSecuritas certified for enterprise compliance such as ISO and SOC2?
Yes. xSecuritas is certified with ISO 27001:2022 and SOC 2 Type II.